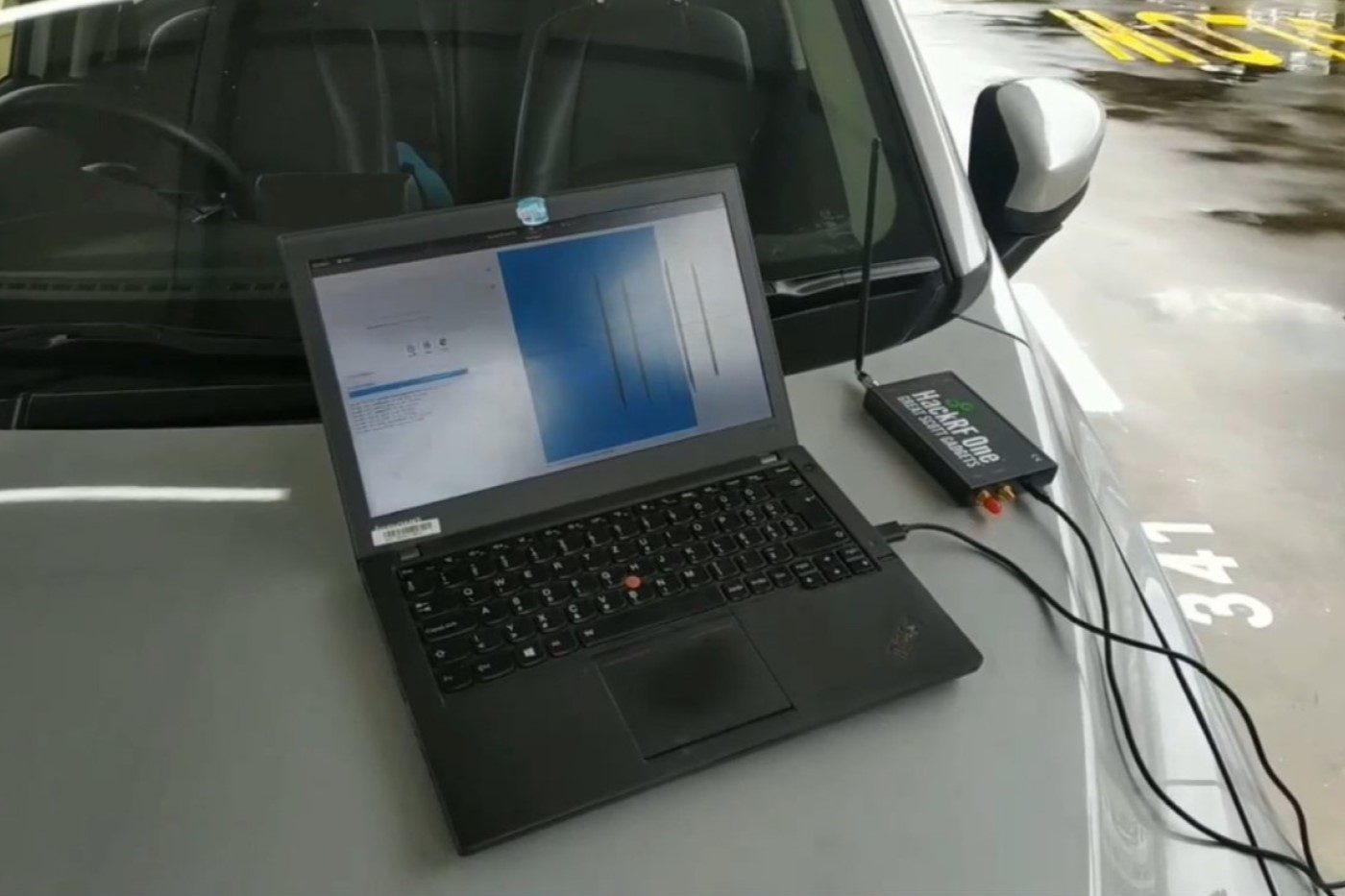
© Black Hat 2022 / Demonstration of the “RollBack” attack
Honda, Kia, Mazda, Hyundai, Nissan… Cars from these suppliers are quite easy to unlock due to a flaw in the contactless keys. The origin of the problem is currently unknown.
At the Black Hat 2022 conference, researchers from the University of Singapore again highlighted the low level of security of remote car door unlocking systems. Also called a “plip”, this small remote control that you attach to your keyring allows you to open and close the vehicle with a simple press of a button.
This system, as we know, is far from excellent. With each button press, a different code is sent to the car, to protect the system against replay attacks. But in 2015, the hacker Samy Kamkar had already shown, with his “RollJam” attack, that this protection was not worth a nail. If the pirate scrambles the transmission with the car, the motorist will necessarily press his button several times. It is then enough for the hacker to intercept two codes.
The magic of resynchronization
It will then transmit the first code to the car to allow the motorist to access it as if nothing had happened, but will keep the second for later use. Indeed, since this code has not been used, it will remain valid… provided of course that the motorist does not send other signals in the meantime. Which is, after all, quite likely if the motorist goes for a ride. This is why this hack is ultimately quite theoretical.
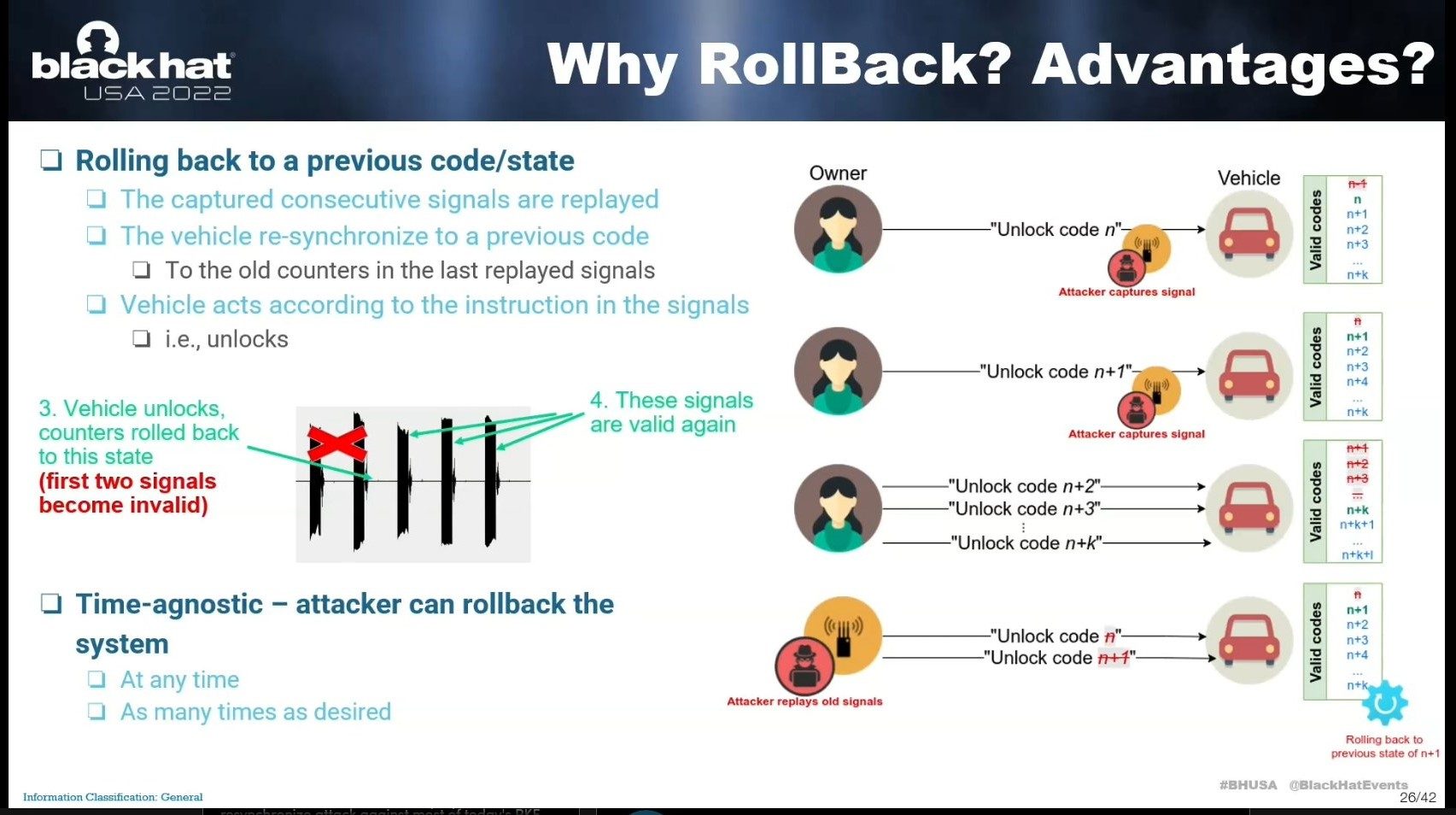
But researchers at the University of Singapore have found a significantly more effective variant. Called “RollBack”, it consists of passively recording a series of codes sent, and that’s it. As weird as it may sound, if the hacker sends these codes back to the car, it will resync to that old serial and ultimately accept the unlock. And this replay can be done at any time. Whatever the actions that the motorist will have made in the meantime, it works every time and as many times as you want. It is magic.
This hack, however, does not work with all cars. It would seem that only Asian manufacturers are concerned. According to the tests carried out by the researchers, the brands Mazda, Honda, Kia and, in part, Hyundai and Nissan are vulnerable. Toyota brand cars, on the other hand, do not seem to be affected by this problem.
What is even stranger is that the number of codes that must be registered is variable. For some cars, it is enough to have two, and it is not necessarily necessary that they are consecutive. In the other cases noted, it takes three or five, and in this case, they must be consecutive. On the other hand, the series can be a mixture of lock and unlock codes, it is not important. In short, the operational conditions are quite diverse.
Beware of car sharing
Being able to save so many codes in a row is not necessarily very simple, but if the hacker has a jammer and is armed with patience, it is quite possible. The most risky situations are those where contactless keys circulate through many hands: valet services, rental agencies or sharing networks. The latter case is particularly risky, since the ignition key is usually in the car. The hacker can then not only unlock the car, but also drive away with it.
The researchers contacted the manufacturers mentioned above, but for the moment, it has not been possible to find the origin of this problem. It could be related to the process of enrolling a new key. When a motorist loses his key and gets a new one, it must be synchronized with the car. Certain behaviors observed during attacks suggest this type of process. But it is impossible to go further at present, because researchers do not have access to the source codes of the on-board computers of the vulnerable cars. ” This is totally owner. At our level, we can only do black box type analyses”the researchers pointed out.
Motorists, for their part, cannot do much either. The only solution would be to stop using plips, but that’s not always possible.
Black Hat 2022