|
1
|

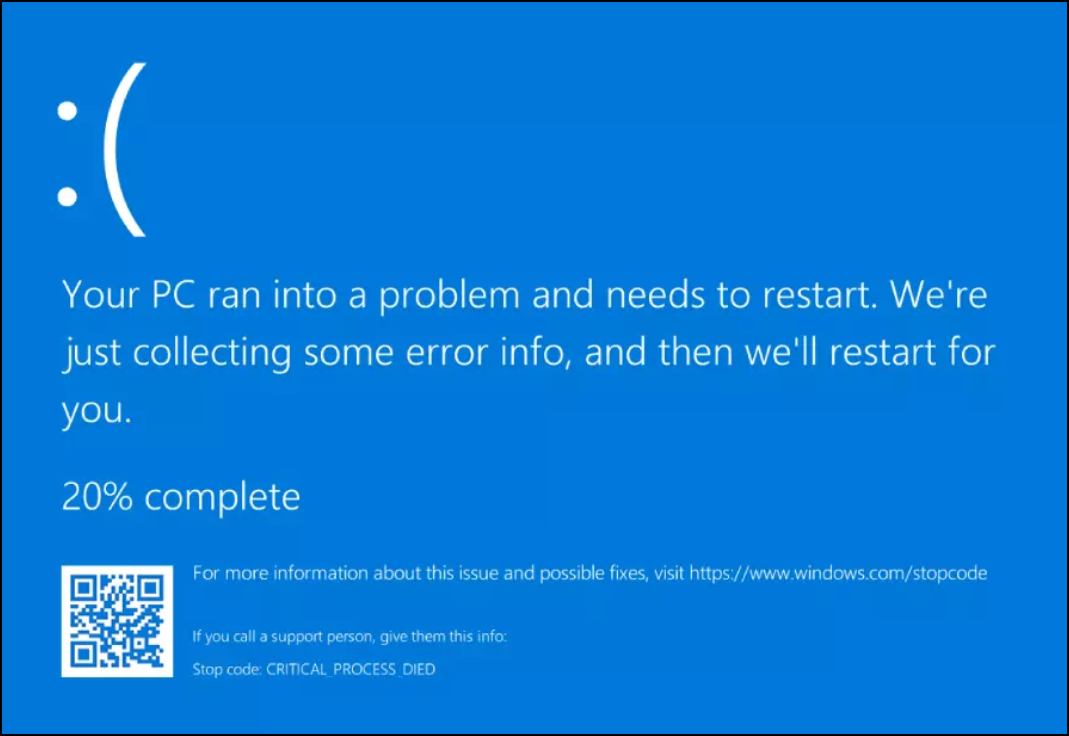
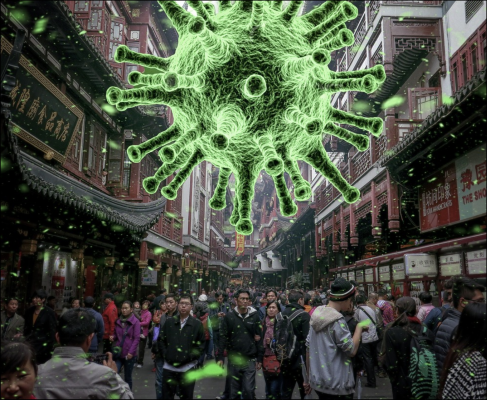
Speaking of Crowdstrike.
What is the name of the software that failed?
A: Eagle
B: Falcon
C: Snowman
|
|
2
|
Which specific operating system went down
when Crowdstrike’s software blundered?
A: Linux
B: MacOS
C:Windows
|
|
3
|

What is Crowdstrike’s home base?
A: Jerusalem, Israel
B: Austin, United States
C: Volgograd, Russia
|
|
4
|

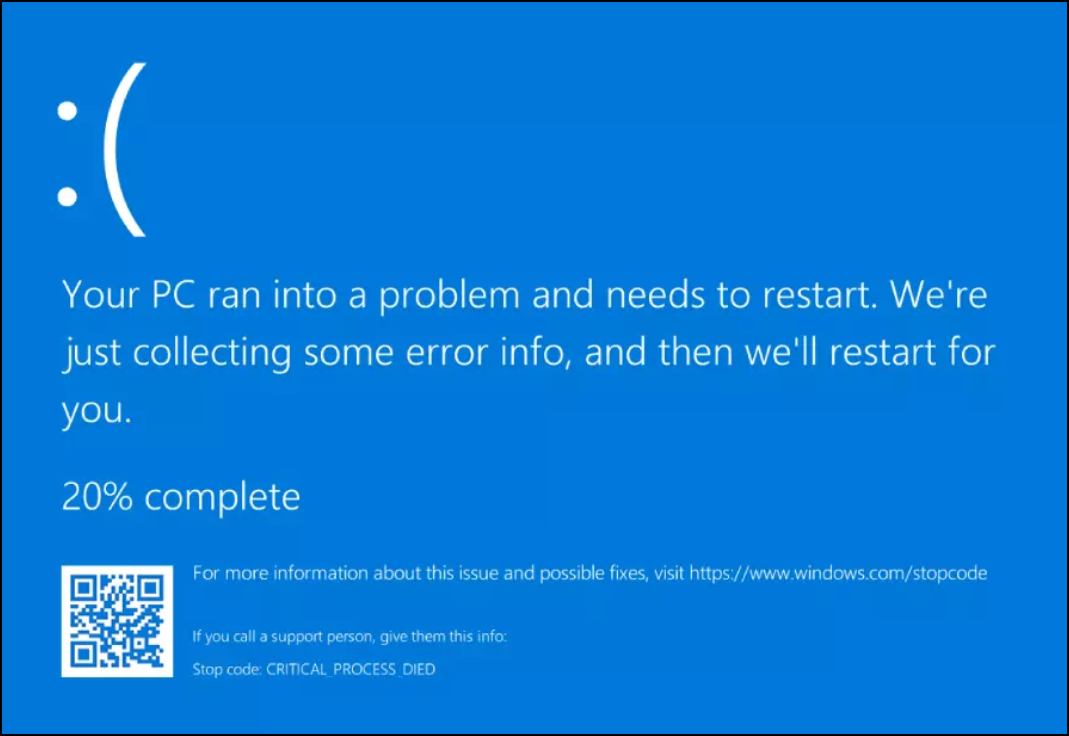
The boot sector virus seems to no longer exist. Why not?
A: A boot sector virus only works if there is
of MS-DOS as the operating system
is used
B: Creating new versions of Windows
no more use of a boot sector
to boot
C: A boot sector virus is spreading
via floppy disks. And become floppy disks
in 2024 (almost) no longer used
|
|
5
|

A boot sector virus is activated
once you get an infected floppy
into the disk drive.
A: Yes
B: No, you need the program for that
start that is on that diskette
C: No, the virus only starts when you open the
computer from that infected one
floppy boot
|
| 6 |
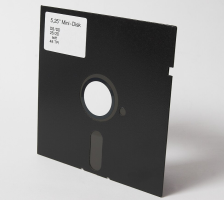
A boot sector virus only works with floppy disks.
A: Yes, with all types of floppy disks
B: Yes, but only with 5¼ inches
diskettes
C: No, a boot sector virus is possible
itself through everything that a Master Boot
Record has spread
|
|
7
|
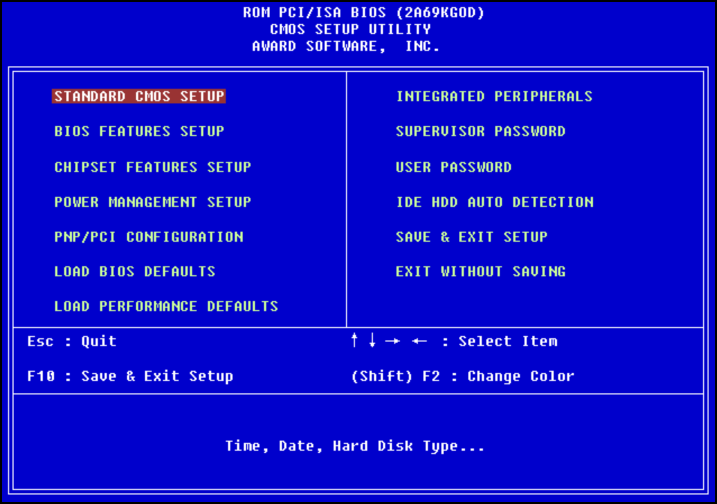
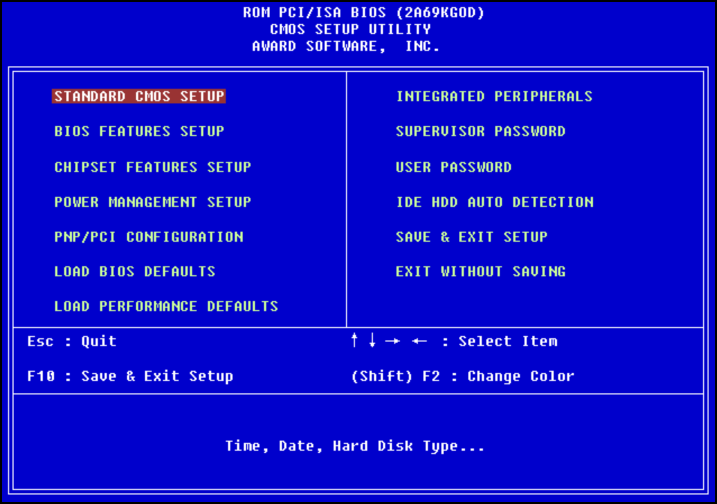
Can the BIOS protect you
against the attack of a boot sector virus?
A: No
B: Partially. The boot sector can be accessed through the BIOS
are secured, but in some cases
that security needs to be improved for a while
disabled
C: Yes
|
| 8 |

What was the first anyway?
computer virus ever created?
A: BlackJack in 1969
B: Creeper in 1971
C: Stoned in 1973
|
| 9 |

What was the first IBM compatible
pc bootsector computer virus
ever made?
A: Brain in 1986
B: Rabbit in 1987
C: Animal in 1988
|
| 10 |

What is the trick of a virus
that spreads via a Trojan Horse?
A: Such a virus resides on a host computer
and infects the other computers
that are found in the same network
B: Such a virus hitches a ride with – often –
popular program. As the host
being installed or started,
then the virus is co-activated
C: Such a virus is deliberately installed from
a USB stick. The USB stick is therefore the host
|
|
11
|

What percentage of email messages
that we classify as spam,
contains some form of malware?
A: 30 percent
B: 60 percent
C: 90 percent
|
| 12 |
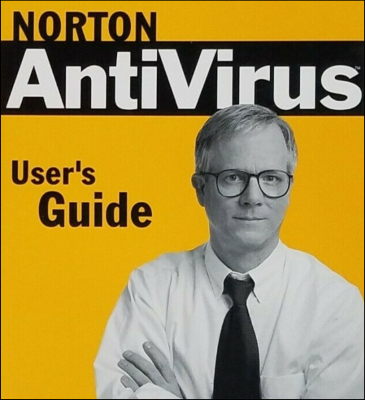
In what year was the famous Norton AntiVirus
came onto the market?
A: 1988
B: 1990
C: 1992
|
|
13
|
What is a macro virus?
A: A virus of enormous (= macro) size
which can occur in different ways
spread
B: A virus that becomes active when you click on a
press a certain key combination
C: A virus written in the macro language
from a popular program,
for example Microsoft Word
|
|
14
|

What is the most famous macro virus
up to this moment?
A: The 1999 Melissa virus for
Microsoft Word
B: The 1993 Christina virus for
Lotus 123
C: The Candy virus from 1988 for
WordPerfect 5.1
|
| 15 |

Which computer virus has the largest
causes financial damage?
A: MyDoom
B: ILoveYou
C: Sobig
|
16
|

Which is to this day
the fastest spreading computer virus
been?
A: MyDoom
B: ILoveYou
C: Sobig
|
| 17 |

What is the most used in 2024?
medium to spread viruses?
A: Freeware
B: E-mail
C: FTP
|
| 18 |
What is the name of the construction?
that actually activates the virus?
A: The ‘infection mechanism’
B: The ‘trigger’
C: The ‘payload’
|
| 19 |

Which type of virus runs continuously
in the working memory (RAM)
from the computer?
A: An executable virus
B: A sleeping virus
C: A resident virus
|
| 20 |

What is a stealth-virus?
A: A virus that attacks unexpectedly
B: A virus that does everything it can
especially not to become
detected
C: A virus that constantly mutates |