How hackers use the botnet to mine cryptocurrencies

Suppose you forget to update or properly secure an Internet-connected server or web application. In that case, chances are that a cryptocurrency mining botnet will infect it first, long before any hacker group in the nation.
Cryptocurrency mining botnets have plagued the internet for the past three years. New botnets are created and discovered regularly despite the more than saturated space. It’s mainly due to the unquenchable thirst of cybercriminals for easy and fast money.
What are cryptocurrency mining botnets?
Botnet mining uses malware to take over the CPU of a device to mine cryptocurrency. Hackers deploy malware that does the job of mining cryptocurrencies and sends it to a shepherd bot, a remote attacker.
The term «botnet» is a combination of the words «robot» and «network». Botnets that target cryptocurrencies are called botnet miners. These systems let their creators mine cryptocurrencies at the expense of unsuspecting device owners who don’t understand their machines are being used.
«Monero is the most popular cryptocurrency for these types of activities,” says Matt Downing, chief analyst at cybersecurity firm Alert Logic. Most likely due to its liquidity and the fact that it is significantly easier to mine than Bitcoin or Ethereum». On the platform ICOholder you can get more information about different types of crypto coins.
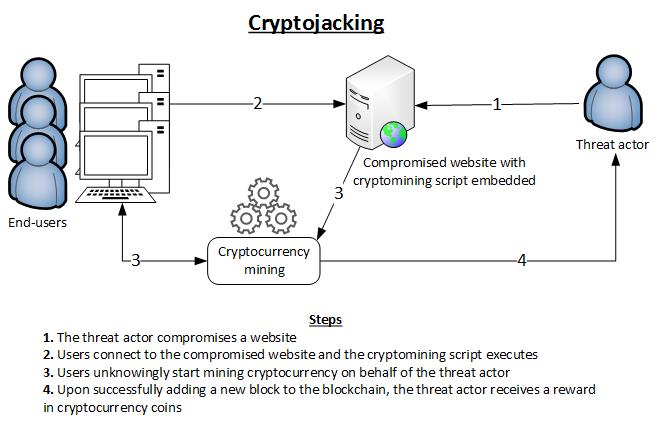
Using botnets for cryptocurrency mining or «crypto-jacking» does not require interaction between the perpetrator and the victim. And instead of attacking and running for high profits, they provide a sustainable way to make money slowly – as long as the botnets remain undetected.
It’s a long-term, low-risk way to save money. The payout isn’t high or immediate, but just like the Monero attacks, patient players in the space can earn millions over time if they’re smart about it.
Overclock the victim’s CPU to 100 percent, and they risk permanently damaging the device. It would be useless for the miner and a huge wake-up call for the victim. But tune your CPU enough to mine over time, and you’ll make consistent profits.
Basic principles of botnet mining
The botnet system is similar to standard computer malware. Computer malware is just like any other computer program, but it is designed to use computers in illegal activities such as damaging systems, destroying or stealing data, etc. These manipulations can harm the device, data, network, and users.
Botnets are automated programs developed by their creators in the form of lines of code and designed to infiltrate a user’s device. Botnets use machine power, electricity, and internet bandwidth to perform certain functions. Common botnet activities include:
- distributed denial of service (DDoS) attacks,
- intrusion orientation,
- financial irregularities,
- email spam.
Botnet mining is used to steal cryptocurrencies. Such a botnet is typically released on a private network of interconnected computers. It then uses the combined power of the devices, resulting in more processing power. It can improve mining performance and corresponding rewards for botnet creators.
If the antivirus or programs installed on the device don’t detect the malware, it is launched without the owner’s knowledge. It is generally capable of playing itself to other connected devices on the network.
Alarm signals for business
It’s easy to infect machines; botnets can infiltrate a computer through phishing campaigns, a hacked website, or even software downloads. And they can go unnoticed if the CPU usage is not too high.
According to Downing, «The immediate impact on the business is that instead of your servers doing what you want them to do, they are running 100% mining Monero for someone».
However, unlike malicious viruses or data theft, businesses can view these attacks as a wake-up call. CPU mining botnets themselves are as much of a problem as the very fact of their infiltration.
«It is important to note that the sole purpose of these botnets is to mine coins. There seem to be no secondary goals. As mining botnets pale compared to other viruses, the severity of these attacks is debatable» – Downing says.
The most notorious botnet attacks
In January 2018, hackers used Alphabet Inc’s Google (GOOGL) DoubleClick advertising services to distribute cryptocurrency mining malware to many European and Asian users. A month later, a botnet called Smominru hijacked more than half a million computing devices. He made machines mine millions of dollars worth of cryptocurrencies.
Another crypto-jacking botnet called Sysrv-hello appeared at the end of 2020. Sysrv-hello is aimed at enterprise web applications and is deployed on Windows and Linux systems. Like other botnets, it has constantly evolved to stay ahead of security researchers and law enforcement. The highly aggressive Sysrv contained elements that found and disabled other cryptocurrency mining botnets.
Protection options from botnet miners

In most cases, proper patch management and cyber hygiene can prevent companies and individuals from getting infected. «Simply patch management would stop 90 percent of all these attacks, and in most cases, we are lucky. Destructive malware or data theft would be far more horrific and use the same vector. If you don’t pay, you are probably using coin miners, and you may not even know it» – Downing warns.
Suppose you are worried about your personal computer being targeted. In that case, you can install an antivirus or ad blocker or use another application, for example, NoCoin or minerBlock as a plugin for Chrome.
Even if your system is infected, the code behind cryptocurrency mining botnets is fairly simple and should be easy for most system administrators to remove.
So, for now, these mining botnets seem like nothing more than a nuisance, but the potential for much more severe attacks certainly exists. If they can take over a smartphone or computer, they can just as quickly take over the cloud, steal resources, disrupt business, and compromise data and intellectual property. How to recognize if you have a botnet? Botnets target cryptocurrency users and miners. Your Internet connection may slow down, your computer or server may slow down, or you may experience high CPU or GPU usage when your hardware is idle. You also won’t be able to close or uninstall specific programs or upgrade your operating system. Antivirus and malware with up-to-date definitions will help you detect it.